EasyAs123.IT is a private Canadian carrier with the ability to track, qualify, triage, and escalate priority based requests, EasyAs123.IT uses Enterprise Class Ticketing Systems. These are very costly and are in a perpetual state of sharpening to keep the unique surgically precise support structure we have. This makes us unique as we have a dedicated site lead for each client with an emergency secondary for redundancy. This keeps all of the critical operational alignments in check, streamlining the synergy of a successful partnership with all of our clients. As such we offer access to all of our services to help aggregate costs for your company and have all the benefits of an aggregated team. It is a proven success, and you are welcome to ask our customers directly about our exceptional services. There is no task too large, or too small, that our team of technical Champions cannot handle effectively.
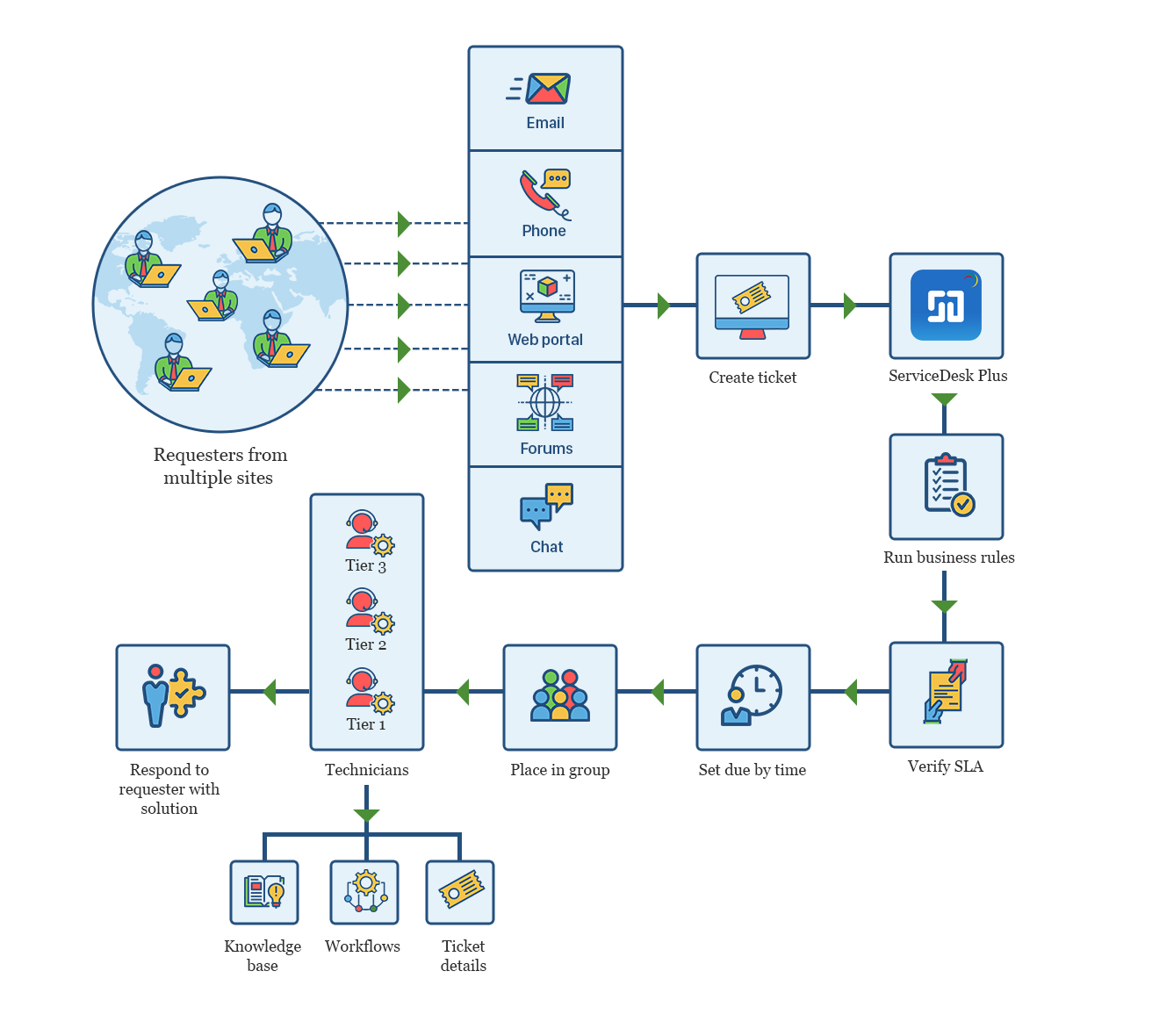

Professional Call Center Services
A 24/7 live agent answer and messaging service is a proven and cost-effective method for businesses to handle calls when staff is unavailable. Recent statistics from Forbes magazine show that 80% of callers sent to voicemail do not leave messages because they don’t believe they will be heard. An answering message service is more than just someone answering your valued customer’s calls, a 24/7 live answering service is an extension of your business. Our professional staff at EasyAs123.IT will ensure your callers are greeted by a courteous and helpful voice and will ensure you receive accurate messages promptly.
Carrier Grade Monitoring
Operating System (OS) Monitoring with EasyAs123.IT provides complete monitoring of desktop and server operating systems – including system metrics, service states, process states, performance counters, event logs, applications (IIS, Exchange, Apache, MySQL, etc), and services (Active Directory, DHCP, Send mail, etc). EasyAs123.IT supports monitoring of Windows, Linux, Unix, Solaris, AIX, HP-UX, and Mac OS/X operating systems. Some of the benefits of Implementing effective operating system monitoring with EasyAs123.IT offers the following advantages. Increased server, services, and application availability. Fast detection of network outages and protocol failures. Rapid discovery of failed services, processes and batch jobs. EasyAs123.IT provides monitoring of all mission-critical infrastructure components on any operating system. High-efficiency worker processes allow for nearly limitless scalability, monitoring effectiveness, proactive alerting, availability reporting, and comprehensive monitoring.


24/7 Emergency services
24/7 live answering service and emergency technical support services for critical application or critical service delivery systems. As well as Emergency Response in the event of any situation, may it be a municipal emergency, oil and gas emergency or any type of event that requires emergency action. Help Desk Support when businesses need excellent help desk or customer service support they rely on EasyAs123.IT agents to log trouble tickets or offer tiered support utilizing our customizable forms software. Virtual Reception, do you require a receptionist but it isn’t in your budget or your call volume doesn’t warrant the expense? All calls answered in your company name 24/7 Whatever the case may be, it is proven success, you are welcome to ask our customers directly about our exceptional services. There is no task too large, or too small, that our team of technical Champions cannot handle effectively.
Data Security Auditing
The objective of this assessment is to determine, what assets are exposed to the public? What information is available in the public domain? What vulnerabilities could a motivated entity discover? What is the operational risk to the business as a whole? EasyAs123.IT Security team will scan, all 65,535 ports of all applicable IP segments for potential security flaws. Examine their system with over 27,000 vulnerability tests for security weakness, including Windows/Linux-based attacks, Denial of Service / DoS attacks, Root Exploits, CGI Abuses, Mail Server Vulnerabilities, Patch Systems checks, Virus Definition checks and Firewall Vulnerabilities. We Use risk Assessment scale to score the risk. The audit objective is to obtain assurance on the systems and network security controls in place that would ensure compliance with IT Security Governance and industry best practices for organizations of similar size and function. Also, the objective of this review is to ensure adequate controls are in place over the IT infrastructure including systems, network, firewalls and segregation of duties and permissions. This process is proven a success, and you are welcome to ask our customers directly about our exceptional services.


Backup & Disaster Recovery Auditing
EasyAs123.IT is called in to deal with critically sensitive forensic Data Security breaches of all sorts, from Hardware Failure, Natural Disasters, Theft, and Ransomware, we are always on the verge of that total catastrophic data threat from all directions. It is imperative that all of the backup and disaster recovery mechanisms are fully functional and being accurately monitored. EasyAs123.IT offers full internal and external Backup, Disaster Recovery auditing to ensure your business-critical data is SAFE so that you can sleep at night. We guarantee that 24/7 protection and retention policies are functional and reliable in the assessment or it is a hard fail. We use certified industry standard methods and techniques to qualify the risk factors. This process is proven a success, and you are welcome to ask our customers directly about our exceptional services. There is no task too large, or too small, that our team of technical Champions cannot handle effectively.
Network Assessment Auditing
The actual fabric of the nervous system for all communications, start at the network layer. If it is a tin can connect to another tin can with a string, or the Canadian national fibre optic network LINK ( http://weathermap.canarie.ca/cds/index.html ) Every single one and zero counts. EasyAs123.IT and our team of certified senior network subject matter experts can use industry standard auditing practices to identify all of the peskiest pinch points that typically slip past the competition. Ultimately networks are mathematical, and math is perfect. So if you truly know what you are doing there is ZERO mystery, it is a perfect science. With our auditing techniques, we can provide a redundant Network Audit. EasyAs123.IT understands creating and maintaining a successful and efficient network begins with a thorough assessment. The network assessment will provide a wealth of information about your network environment and highlight challenges in areas that typically are neglected.


Employee Security Awareness Training
Comprehensive Training for Your Employees, it is the Most Vulnerable Entry Point for Cyber Attacks and Ransomware. EasyAs123.IT Security Team Awareness Training teaches your employees to identify vulnerabilities and threats to your business operations quickly.
Protecting your company’s network and data from malicious threats begins with ensuring your employees recognize and avoid threats that appear in their emails, browsers, and on their wireless devices. Even the best security technology can’t protect you unless employees understand their roles and responsibilities in safeguarding sensitive data and protecting company resources. In addition to avoiding threats to your network, you and your employees also have legal and regulatory obligations to respect and protect the privacy of information and its integrity and confidentiality.
IT Staffing and IT Augmentation
EasyAs123.IT realizes that there is an increasing drive to reduce costs and improve operational efficiencies through technological innovation. This naturally translates into a growing number of IT projects, where success or failure of a business can often hinge on the ability to complete these projects on time, within budget, and to specification. Developing in-house capabilities to complete these projects can be a costly and risky venture, particularly when the IT needs of an organization are constantly changing. Moreover, in today’s business world where falling behind the IT innovation curve can lead to disaster, very few companies have static IT needs. Even companies who are content with IT business, as usual, can easily find themselves relying on outdated legacy systems which, upon failure, could cripple an industry. When companies look for outside help in completing IT projects, they are generally considering two delivery models: staff augmentation and project outsourcing. IT staff augmentation allows a company to add staff to their teams based on the additional skills required to support their initiatives.


vCTO and IT Management
EasyAs123.IT vCTO is becoming a staple for all successful companies, of any size, in any industry. Once thought of as a luxury, it is now essential to have this tech-savvy, business-minded professional on your side and on your leadership team. In recent conversations with other business owners about CTOs, I realized just how vital this role is, especially for small business longevity and success. A Chief Technology Officer, sometimes called a Chief Information Officer, is responsible for overseeing all technology use and implementation for the company. This individual should be able to understand what technologies help employees become productive and do their jobs, which technologies can increase process efficiency, which technologies are just a fad, and ways to improve the overall operation through strategic tech implementation. In order to do this job well, an individual has to have a firm grip on your unique operation and have a head for goals alignment. A good CTO will also have industry-specific knowledge.
Custom Web and App Development
Data management solutions are only as useful as their core design. That’s why we strategically construct custom database-driven web applications with the end-user and your organization’s unique needs in mind.
We specialize in building custom web applications that utilize relational databases, dynamic functionality, and interfaces designed for optimal user experience. Whether you need a simple interactive directory or sophisticated business functions that integrate with other systems, we can tailor a solution to your requirements.
Let’s Talk
If you have a web application project in need of development, let’s talk. We’d love to learn more about your requirements and see if we might be a good fit to work together.

Flexible Technologies and Frameworks
Our custom web applications can be built on several technologies and frameworks, including PHP & MySQL, Zend framework, CodeIgniter framework, .NET & SQL. We can also integrate applications with popular website content management systems (CMS) such as WordPress, Drupal, Expression Engine and others.
Custom User Interface Design
Your web application is of little practical use unless it is easy for the intended audiences to use. All of our web applications utilize a custom interface that is designed for both usability and aesthetics – matched to your brand standards and optimized for the needs of target users.
Administer Dashboards
Our applications utilize custom-designed dashboard control panels, giving your application’s administrators full control over data management and custom functions.
Cloud-Hosted
Our web applications are hosted in the cloud for easy access over the web by virtually any Internet-connected device with the appropriate permissions.
Mobile-Friendly
Our web application interfaces utilize responsive design so that they can be accessed by users across a range of modern devices – from a desktop, to tablet, and handheld smartphones.
Integration with Websites and Other Applications
Oftentimes a web application doesn’t live as a stand-alone technology but rather needs to be integrated with a larger web presence or other 3rd party systems. No problem; we can build web applications to seamlessly integrate with your website, or even build an entirely new website around your web application. We can also integrate with APIs to play nicely with other applications.
Data Management & Reporting
If your web application collects data, you’ll want it to be accessible, which is why we make it easy to export your data or integrate with other systems. We can also make it easy to keep track of utilization with performance reports and custom views to suit your data collection and reporting needs.
Security and Access Control
Web applications can also be secured for multiple levels of access with permissions and unique logins, or hosted on a private network, according to your access requirements.
Fully Supported
Once your web application is developed and deployed, we remain on your team for ongoing support and troubleshooting, and for future development and enhancements, as desired.
Markets Served
Our custom database projects span a variety of industries, including healthcare, education, membership associations, non-profits, consulting groups, private businesses and technology start-ups.

E-commerce
What is Ecommerce?
Ecommerce, also known as electronic commerce or internet commerce, refers to the buying and selling of goods or services using the internet, and the transfer of money and data to execute these transactions.
Ecommerce is often used to refer to the sale of physical products online, but it can also describe any kind of commercial transaction that is facilitated through the internet.
Whereas e-business refers to all aspects of operating an online business, e-commerce refers specifically to the transaction of goods and services.
The history of e-commerce begins with the first ever online sale: on August 11, 1994 a man sold a CD by the band Sting to his friend through his website NetMarket, an American retail platform. This is the first example of a consumer purchasing a product from business through the World Wide Web—or “e-commerce” as we commonly know it today.
Since then, e-commerce has evolved to make products easier to discover and purchase through online retailers and marketplaces. Independent freelancers, small businesses, and large corporations have all benefited from e-commerce, which enables them to sell their goods and services at a scale that was not possible with traditional offline retail.
Global retail e-commerce sales are projected to reach $27 trillion by 2020.
Types of E-commerce Models
There are four main types of e-commerce models that can describe almost every transaction that takes place between consumers and businesses.
- Business to Consumer (B2C):
When a business sells a good or service to an individual consumer (e.g. You buy a pair of shoes from an online retailer). - Business to Business (B2B):
When a business sells a good or service to another business (e.g. A business sells software-as-a-service for other businesses to use) - Consumer to Consumer (C2C):
When a consumer sells a good or service to another consumer (e.g. You sell your old furniture on eBay to another consumer). - Consumer to Business (C2B):
When a consumer sells their own products or services to a business or organization (e.g. An influencer offers exposure to their online audience in exchange for a fee, or a photographer licenses their photo for a business to use).
Examples of Ecommerce
E-commerce can take on a variety of forms involving different transactional relationships between businesses and consumers, as well as different objects being exchanged as part of these transactions.
- Retail:
The sale of a product by business directly to a customer without any intermediary. - Wholesale:
The sale of products in bulk, often to a retailer that then sells them directly to consumers. - Dropshipping:
The sale of a product, which is manufactured and shipped to the consumer by a third party. - Crowdfunding:
The collection of money from consumers in advance of a product being available in order to raise the startup capital necessary to bring it to market. - Subscription:
The automatic recurring purchase of a product or service on a regular basis until the subscriber chooses to cancel. - Physical products:
Any tangible good that requires inventory to be replenished and orders to be physically shipped to customers as sales are made. - Digital products:
Downloadable digital goods, templates, and courses, or media that must be purchased for consumption or licensed for use. - Services:
A skill or set of skills provided in exchange for compensation. The service provider’s time can be purchased for a fee.
Frontend & Backend Development
Get a fully functional site that has everything you need to attract visitors, increase sales, and improve your image.
Most websites have two ends; the frontend and the backend. These parts of the website are what makes them function the way they do so that visitors don’t have trouble accessing information.
EasyAs123.IT specializes in frontend as well as backend development.
Frontend development
EasyAs123.IT keeps up with the latest trends in front-end development to meet the growing user demands for simplicity and visual appeal. To make web applications not only powerful but also interactive, intuitive and stylish, we work with a wide range of technologies:
| Languages and techniques: HTML, CSS, JavaScript, Ajax, jQuery;
Frameworks: Bootstrap, Foundation, Backbone, AngularJS, EmberJS, ReactJS, MeteorJS. |
Backend development
We define our backend development tools in accordance with our customers’ business requirements and develop robust and durable backends, irrespective of the technologies we use. For convenient further administration, we also offer deployment and customization of a suitable content management system.
| Languages: PHP, Python, .NET, Java, JavaScript (NodeJS);
Frameworks: Symfony, Zend Framework (for legacy web app maintenance), Laravel, Django, Pyramid, ASP.NET, Spring, Express; CMSs: Drupal, Pimcore, WordPress. |

SEO Online Marketing | Media
EasyAs123.IT Helps You Take Advantage of All the Digital Marketing Tools Available To Drive Traffic to Your Website and Remain Competitive.
Did you know that 90% of users don’t look past the first 10 search engine results? Have you ever wondered what it would be like to get into that top 10 for a specific keyword? We use all the latest SEO techniques to get your business in the top 10 results for relevant keywords.
EasyAs123.IT we work together with our clients to plan out and implement an extensive strategy to boost your website in the rankings. We have flexible packages available, tailored to your budget and your needs. We specialize in helping small businesses boost their online presence and get found on not only Google, but all major search engines.
With a 90% client retention rate, along with a consistently ROI positive track-record, and an unparalleled focus on customer service, we truly believe we are among Canada’s best SEO providers!
Our standard SEO process:
Website Audit
We will scan your entire site and find where we can optimize and make technical changes to improve rankings.
Industry Analysis
We will research industry sector, marketing and sales trends.
Competitive Analysis
We will conduct a review of competitor sites.
Keyword Research
We will undergo thorough research for targeted keyword terms.
On-Site Optimization
We will implement extensive technical changes including title tags, meta tags, copy and internal linking.
Link Building
We will gain links from niche websites, through various strategies.
Monitoring & Reporting
We will monitor your site’s rankings and progress and report monthly.

